Tactics 101: 026. Cordon and Search Operations
ORGANIZATION
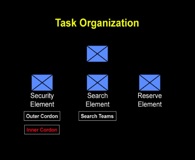
Whether you consider yourself a neophyte or a master tactician, executing a cordon and search is a thinking man’s game. The challenges of a complex urban environment can make your brain hurt just a bit. The skilled tactician will disregard this pain and begin planning for success. One of the first things to plan is your task organization, so let’s begin by understanding the task organization of battalion or company cordon and search operations. There are many variations on task organizing; we will portray one version below.
The typical organization for a cordon and search operation consists of a Command Element, Security Element, Search/Assault Element, plus a Reserve Element to deal with the unexpected.
{default}Command Element
Effective command and control is tantamount for all military operations and no less important during a cordon and search. The Command element is the headquarters of the organization executing the operation. Careful consideration should be given to the size and composition of this element. The Command element should be large enough to effectively coordinate and synchronize the security and search operations but must be small enough to not create an overwhelming footprint and become a burden on overall security. The execution of a cordon and search is no place for a commander to carry a big entourage with him!
The position of the Command element in relation to the search operation is another important factor. Since the focus of the operation is the actual search, the Command element usually positions itself where it will be close enough to the search to carry out its duties but without getting in the way. Normally, the Command element will include host-nation representation in the form of a police or government official, adding legitimacy to the overall operation.
Security Element
The Security element consists of two primary components, the outer and inner cordon. Cordon is a tactical task given to a unit to prevent the enemy’s withdrawal from or reinforcement of a position. A cordon is a type of isolation. It implies seizing or controlling key terrain and/or mounted and dismounted avenues of approach along the search area. Let’s discuss each one of the components separately and then we will tie them together.
Outer Cordon:
The objectives of the outer cordon are to prevent anyone/anything from moving into the designated objective area (search area). This could include enemy reinforcements or even civilians who could disrupt the operation. If you remember our discussion on tactical tasks, this element may utilize any of a number of tactical tasks to accomplish their purpose, including isolate, block, contain, deny, secure, etc. To achieve these tasks, an element may set up traffic control points or blocking positions, emplace snipers, utilize observation posts, and conduct patrols. The commander will determine the various methods to use based on his analysis.
Inner Cordon:
The main objectives of the inner cordon are to protect the main effort of the operation (the Search /Assault Element) from the enemy and ensure the enemy cannot enter or leave the search area. The tactical tasks that may be utilized include those mentioned above in outer cordon and suppress, cover, and guard. The element executing the inner cordon may utilize (among several methods): overwatch positions, support-by-fire positions, and emplacing snipers. One of the major differences in the outer and inner cordon is the amount of terrain involved. Whereas, the outer cordon may require setting up forces along many blocks (or kilometers if in an open environment), the inner cordon may only require a block, a single building, or even a portion of a building.
[continued on next page]


This was an outstanding help to my classes on CS. Thanks for publishing this peice.